Release Notes for STM32 Key Management Services
Copyright © 2019 STMicroelectronics
Purpose
Key Management Services (KMS) provides cryptographic services through the standard PKCS#11 APIs (developed by OASIS) allowing to abstract the key value to the caller (using object ID and not directly the key value). KMS can be executed inside a protected/isolated environment in order to ensure that key value can’t be accessed by an unauthorized code running outside the protected/isolated environment.
The figure below shows the overall KMS architecture.
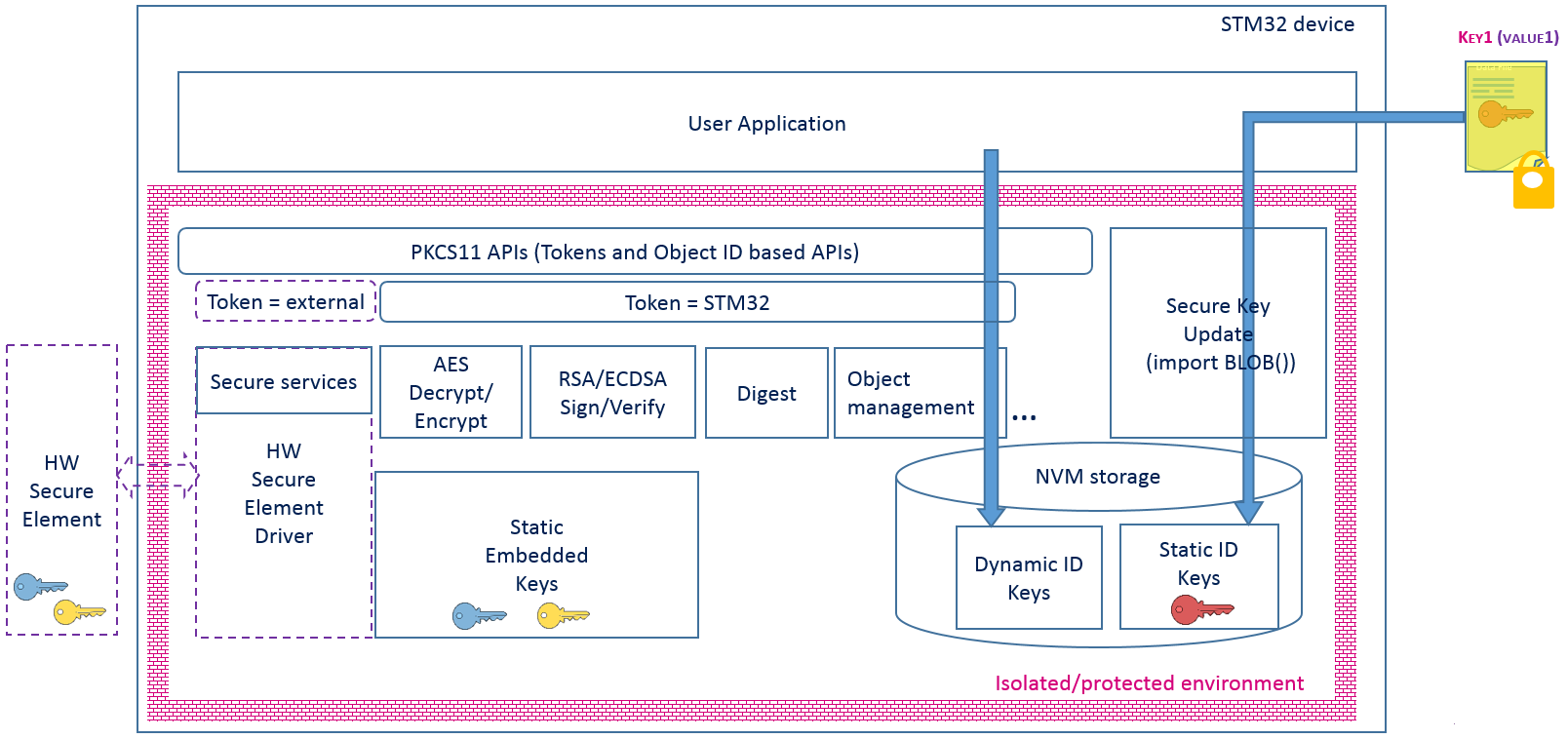
KMS manages 3 types of keys:
- Static embedded keys :
- Predefined keys embedded within the code that can’t be modified
- Unmutable keys
- Predefined keys embedded within the code that can’t be modified
- Updatable keys with static ID :
- Keys IDs are predefined in the system
- Key(s) can be injected or updated in a NVM storage via a secure procedure using Static Embedded Keys(authenticity check, data integrity check and data decryption)
- Key can’t be deleted
- Provisionnable keys
- Keys IDs are predefined in the system
- Updatable keys with dynamic ID :
- Keys IDs are defined when keys are created using KMS services
- Key value can be updated using KMS services
- Key can be deleted
- Runtime keys
- Keys IDs are defined when keys are created using KMS services
KMS supports this subset of PKCS#11 APIs:
- Object management functions: creation / update / deletion / search
- AES Encrypt & Decrypt functions
- SHA Digest functions
- RSA Sign / Verify functions
- ECDSA Verify functions
- ECC key pair generation
- ECDH key derivation
For more details, refer to UM2262 : Getting started with X-CUBE-SBSFU expansion package, Chapter 4.
Update History
Main Changes
New features in this release are :
Secure counters
Give possibility to encrypt the blob objects in NVM
CHM documentation updated
Known Limitations
- None
Backward Compatibility
Compatibility with v1.1.8
Main Changes
- Update LICENSE file for Key Management Services middleware (Software license agreement description)
Known Limitations
- None
Backward Compatibility
Compatibility with v1.1.7
Main Changes
- Create LICENSE file for Key Management Services middleware (Software license agreement description)
Known Limitations
- None
Backward Compatibility
Compatibility with v1.1.6
Main Changes
Give possibility to derivate keys in RAM instead of NVM
Locked objects are no more accessible by searches
Known Limitations
- None
Backward Compatibility
Break of compatibility with v1.1.5
Main Changes
- Minor fix for build issues
Known Limitations
- None
Backward Compatibility
- Fully compatible with previous version
Main Changes
- CHM documentation updated
Known Limitations
- None
Backward Compatibility
- Fully compatible with previous version
Main Changes
- Warnings issues fixes
Known Limitations
- None
Backward Compatibility
- Fully compatible with previous version
Main Changes
Configuration switch placement review
Warnings and spelling issues fixes
Known Limitations
- None
Backward Compatibility
- Fully compatible with previous version
Main Changes
C_STM_ImportBlob update to specify blob download area
Allow multiple C_Initialize and C_Finalize imbricated calls
Known Limitations
- None
Backward Compatibility
- Break of compatibility with V1.1.0 (New parameter C_STM_ImportBlob)
Main Changes
New features and improvements introduced in this release are :
Object search
ECC key pair generation
ECDH key derivation
Memory management improved (introduction of different allocators)
Lock keys and services vendor APIs
iKMS/niKMS folders replaces tKMS one
- Use iKMS when caller is isolated from KMS by a secure enclave
- Use niKMS when caller is not isolated from KMS by a secure enclave
- Use iKMS when caller is isolated from KMS by a secure enclave
MPU isolation support in iKMS
kms_config.h redesign (better scalability and config build time check)
Bug fixes
- AES CMAC moved to Sign/Verify services
- Secure enforcement when using KMS in a secure enclave
- PKCS#11 compliance (returned value, parameters handling…)
- AES CMAC moved to Sign/Verify services
Known Limitations
- None
Backward Compatibility
- Break of compatibility with V1.0.0
Main Changes
First official release
Official delivery of Key Management Services for STM32 series, compliant with PKCS#11 APIs from OASIS.
Known Limitations
None